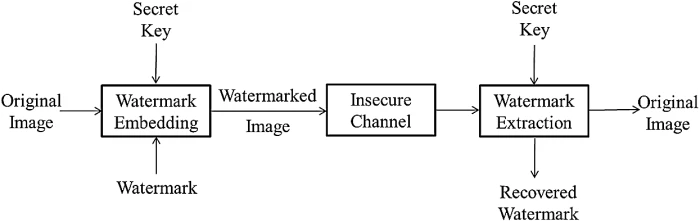
An illustration of the embedding and extraction process for the 2LSB... | Download Scientific Diagram

Joint index coding and reversible data hiding methods for color image quantization | Multimedia Tools and Applications

Buy The Secret of Meta Skill & Neuroscience Book Online at Low Prices in India | The Secret of Meta Skill & Neuroscience Reviews & Ratings - Amazon.in

Wikipedia Link Rot - A Secret Goldmine for Broken Link Building | Link building, Strategies, Local seo
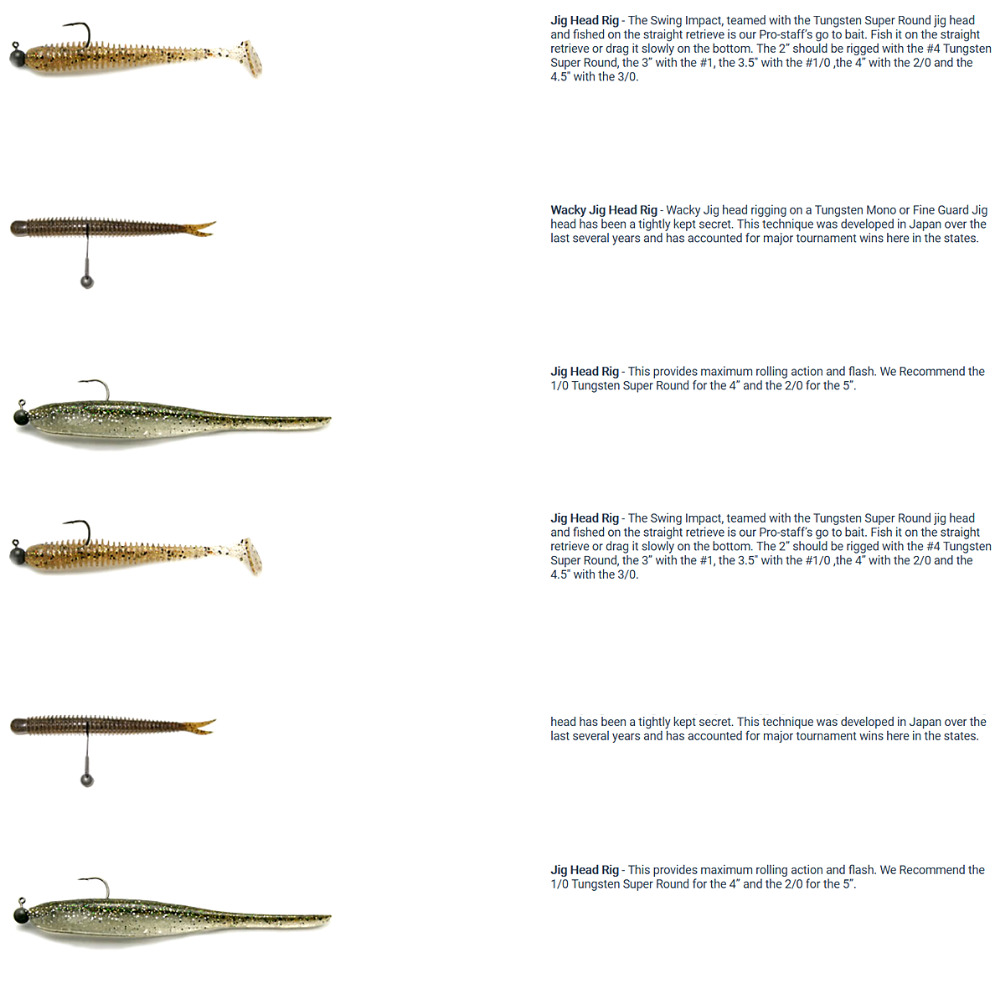
KEITECH Fishing Tungsten SUPER ROUND Jig Head Hook size #2/0 | 24/7-FISHING Freshwater fishing store

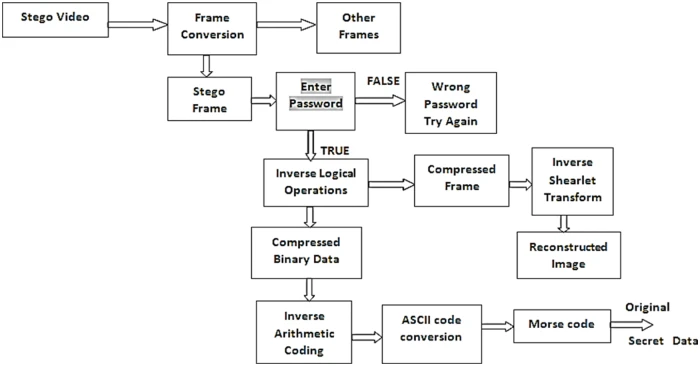
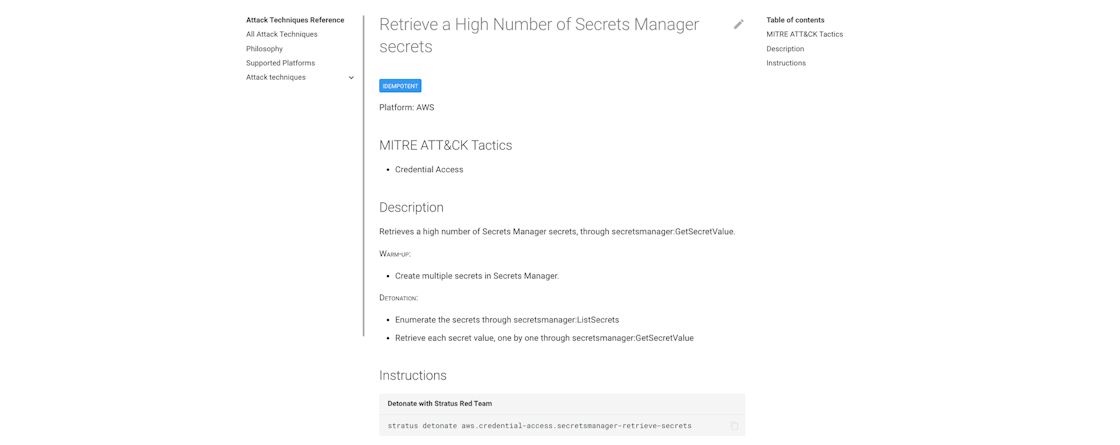
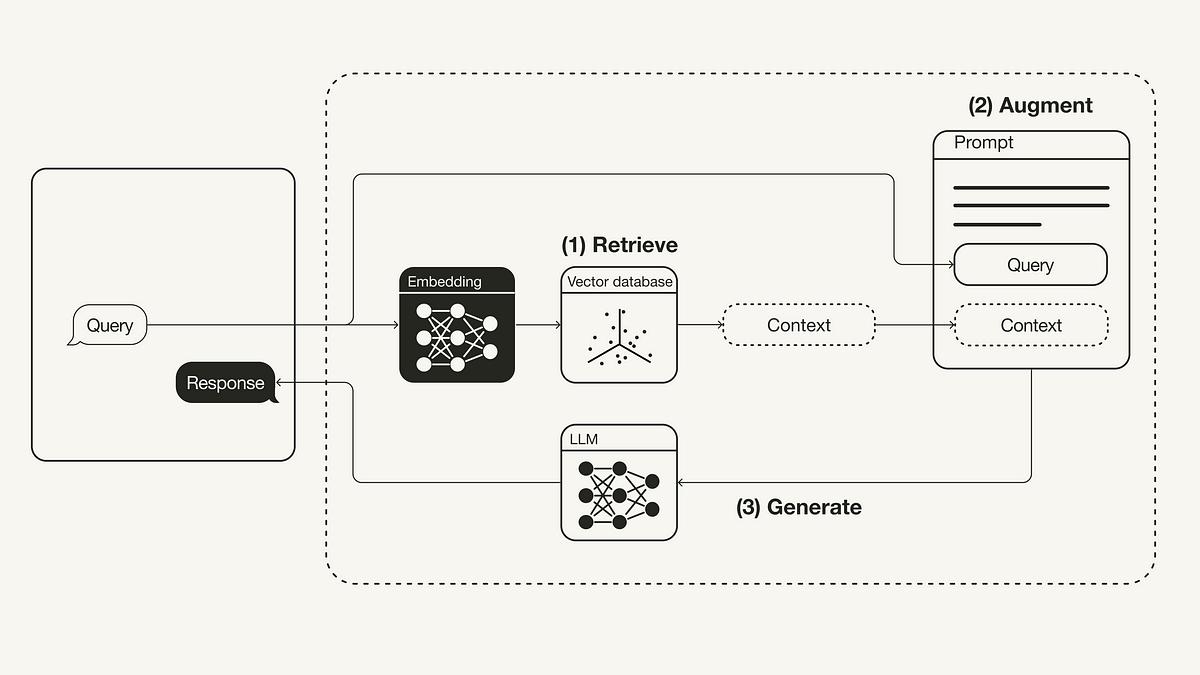
Comprehensive survey of image steganography: Techniques, Evaluations, and trends in future research - ScienceDirect








![KING OF THIEVES A SECRET TECHNIQUE [MUST WATCH] - YouTube KING OF THIEVES A SECRET TECHNIQUE [MUST WATCH] - YouTube](https://i.ytimg.com/vi/vWbv_uHu5qc/sddefault.jpg)





![PDF] IMAGE STEGANOGRAPHY IN YUV COLOR SPACE | Semantic Scholar PDF] IMAGE STEGANOGRAPHY IN YUV COLOR SPACE | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/04a613041a2f4d643bba17057b0d7a6e9e5f5c1d/2-Figure1-1.png)